About 2 months ago we decided to rewrite our client application for Mac OS. One of the new features we had to add was active directory authentication. It took us more time than we anticipated to implement this feature.
Client application for Windows already had active directory integrated. We knew that it worked with no issues based on customers’ reports. But some customers started asking for active directory for the Mac application as well. So here are things we learned while implementing it. There were two steps to implementing active directory:
1 – How to test if our implementation worked? When we implemented the Windows app, an active directory server hosted on the cloud was used for testing. We needed a testing environment for Mac.
2 – What APIs to use? Should we use Mac’s OpenDirectory API for it? Or should we be using openldap API that is cross platform and supports active directory?
Testing is really important part of software development. You have to know how to test each feature of your application. We thought we should set up our own active directory server and create user accounts and use it to test our Mac application. So we setup an Active Directory 2012 R2 on a machine and used it for testing, we had an active directory running. We tried to bind one of Windows laptops to it but the laptop could not find the server. The problem was that DNS server could not find the AD domain name so we had to add AD server IP address as a DNS server. That worked well and the Windows laptop was bound to the AD server. Now, it was Mac’s turn. We did the same thing for Mac, adding IP address of the AD server as a DNS server. We faced another problem with Mac. It was complaining that timeservers did not match. We finally figured out that we had to point the timeserver in Mac to the AD server IP address. Still, the binding process was failing due to a plugin error, which we could never solve. However, when we tried binding, from the status messages of binding process, we could tell that it was able to find the AD server and authenticate the user but fail after those steps. So we thought we do not need to bind the Mac to the AD server. If Mac can do authentication then we can do it as well. We were right!
After dabbling with this issue for more than we should have to get active directory set up on Mac and start implementation. We tried to use OpenDirectory API in Mac to implement active directory authentication but it proved to be very frustrating and had to abandon that route due to limited support and plugin issues Mac OS had. So what should we have done? Python! Believe us, python has API for everything! So indeed, there was one called ldap. We used it to do active directory authentication in Mac. It worked! We looked at its source code and it was C code that was doing most of the core part. We were able to trace the code and saw relevant includes such as #include which grabbed our attention. After researching further, we found out there is actually an API called openldap that is cross platform and supports AD. Why not use that? Ldap python module already has a code that does active directory authentication. So we just learned the function names that should have been used and implemented active directory authentication using openldap C API. At the end of the day, we had around 10 lines of code that took us around 5 days.
All in all, that was a different experience we had. Even though it took us so long to write 10 lines of code, now we support active directory in both Mac and Windows apps and our customers are happy about it. So it was worth it.

Don't miss a Story.
Want to set up a wireless Conference Room?Try Now
Over the last three weeks we have overhauled our Windows client application. This was prompted by the reaching of our MVP (minimum viable product) and our desire to have a code base that is both updatable and easily debugged. In one of our earlier posts, we discussed our belief in the MVC model and significant code modularity. It was that internal debate that pushed us in this direction. It also gave us a good opportunity to revamp the UI and UX with newer and more professional designs.
We began by trying to adapt as much of the previous code as possible. This meant holding to the same Windows development platform: Windows Forms. Remaining on this platform would guarantee the reuse of our business logic and the libraries would remain. Where problems were likely to be found was on the User Interface (UI) end. The first static designs turned out well. It seemed to be no problem following the images given to us by our UI designer from Bolt.io – our first VC and start-up accelerator.
It was in the implementation of specific UI elements, like a customized list, and animations that we ran into significant problems. As there is no native library option for animations it became difficult to move forward on this platform. We were forced to port our code over to Windows Presentation Framework (WPF). With their XAML layouts and native animation APIs, this development foundation is much better suited to building customized, good-looking and smart UIs. Perhaps we were wrong in our preference for WPF UI design tools, but as the lead on our UI development team has a stronger background in mobile development, this was his preference.
Anyway, the trouble was going to be implementing our business logic solutions within this new framework. This was made easier by them both belonging to Windows Visual Studio and therefore being compatible with C# or C++. Also aiding this switch was our decision to modularize the code. It allowed for us to attach it to the front end piece by piece, whereas before it was an ugly fusion of view and logic.
When we finally started we found little resistance from WPF in the execution of our designs. It was, for the most part an easy switch. We only ran into any trouble when piecing together our custom PasswordBox element. We required it to have a placeholder and as far as we could tell the native object did not have such an option. Our solution was to situate a TextBlock on top of the PasswordBox until it is selected, at which point we send “focus” to the PasswordBox and hide the TextBlock. A simple, but hacked together solution.
In all, this was a rewarding experience. We managed to modularize our code, update our design and add animations to what was once a static application. Beyond that we gained experience in the more modern development environment that is Windows Presentation Foundation. The guys at Infragistics still see a use for WinForms and they may be right. However, my recommendation to all, and I wish that we had found this earlier in our prototyping stage, is to move yourself into a future of glossy UIs and responsive UX.

Don't miss a Story.
Calendars are a ubiquitous aspect of workplace communication. As every IT pro would know, they can be hard to setup and manage in a sane and user-friendly manner. It can be especially hard to use calendars efficiently to manage meeting room availability. Meeting rooms that can make their status known to people who enter the room can be very handy. Since most meeting rooms come with a TV screen, it makes sense to display this information on the screen.
In this post, we’ll dive into the internals of Microsoft Exchange Server aka Azure Active Directory aka Office 365 and see how they deal with meeting rooms and calendars.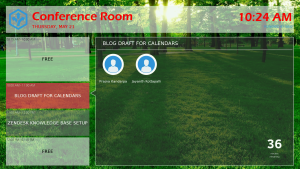
But first, lets see what each of these things mean and how they are different from each other. Exchange Server is Microsoft’s calendar, mail server and directory server(a fancy term for a contact manager). They offer this product as an enterprise solution for companies of all sizes. The server can be configured and setup in-house on the company’s premises with the option to sync data periodically to servers in the cloud. This sync functionality comes in handy when a company has multiple geographic locations and needs up to date inter location communication systems.
There have been multiple versions of Exchange Server over the years (Exchange Server 2003, 2007, 2010, 2013). Since Microsoft loves to maintain backwards compatibility in all their products, this creates interesting problems for people that want to use the APIs offered by Exchange Server to create software services for the companies that use them. At Ubiq, we integrate with the calendar in Exchange Server to display the meeting information pertinent to a meeting room. All Exchange Server versions support a Resource type, which can used to represent meeting rooms, printers and other non-person entities. Resources may optionally also be configured with a Mailbox. For instance, a meeting room resource is not configured with a mailbox by default in some versions of Exchange Server. Resource mailboxes may also be configured to auto accept calendar invitations. Usually, when you add a meeting room email to the Location field when creating an event, the invite gets sent to the mailbox for the meeting room resource which auto-accepts the invite.
Since our customers use a multitude of Exchange Server versions, we’ve had to add support for the various authentication methods used by them. Each of the methods presented different problems. NTLM Authentication is used exclusively for on-premise Exchange servers. They are integrated with the organization’s Active Directory and require the Resources to have mailboxes associated with, inspecific, they need to have authentication credentials, i.e. email ID and password. Unfortunately, the default behaviour of resources such as meeting rooms in Exchange server is that, they do not explicitly have an actual mailbox associated to them. This was tricky to deal with as it would require the organization’s Exchange Admin to create mailboxes to the meeting rooms. In the case where the Exchange Admin cannot approve this request, we had to come up with a different solution to this problem. For the organizations that use Office 365, NTLM is not an option, for this case, we had to work with Office 365’s Oauth REST API. That was straight forward to work with as Microsoft has done an excellent job in following the standard (for once, lol). However, there were a few settings that had to changed to allow REST API calls to get the right information for the resource calendars.
All-in-all it was fun building a solution for calendar integration for the companies that use Microsoft Exchange Server, we are very happy with the outcome of the calendar integration.

Don't miss a Story.
Want to set up a wireless Conference Room?Try Now
A fresh set of eyes can be the needed ingredient to galvanize a reorganization. Being the new member of the Ubiq team positioned me uniquely in this point of view. It was during my introduction to the code-base that I made note, over and over, how the classes were cluttered and the methods too integrated. The code lacked any semblance of modularity or planning. It was shortly after my arrival that we began the restructuring and rebasing of the source code.
We began with two days of meetings discussing structure of the disparate applications: client-side (Windows, OSX, Android, iOS), server-side and web-based. These meetings ranged from methods of synchronization of the client-side frameworks to the positioning of our potential transition to new hardware. It was all-encompassing and sometimes, embarrassing. Our flaws were on display, fault was apportioned, but this enabled us to move forward now and into the future.
This process was enlightening on two levels. First, we quickly came to realize that an overhaul was required. If we were to adhere more strictly to programming principles and best practices our entire base was going to change. Second, we had to determine how we can avoid this/these issue(s) in later iterations, new applications or added features. We surmised that a process had to be developed whereby each new product is executed in a specific set of steps. Largely, this involves engaging in significant and relevant planning. As obvious as our conclusion may seem now, it was not apparent when we, as a fledgling company, set out. This planning had to exist on two fronts: structure and schedule.
The former of the two, structure, is vitally important to any early stage company. Our discussions centered around how to minimize development time. That includes business logic and user interface. Our thinking was that fixing bugs was of the utmost significance to our beta customers. In order to get them to extend our service we have to be able to show them that we are working on their issues. They want to see progress. If one of their issues is solved, invariably, that solves issues for potential future clients. This lead us to the idea that the more uniform the individual applications the more quickly a small team can respond to issues.
Ideally, all could be done in one language with one IDE. Failing that we can do our best to make knowledge of one application translatable to another. Our first decision was to amalgamate the convention upon with the software is based. We restructured on an MVC model. Second, we built up one structure that we were certain could be applied across all platforms. This meant having a single controller, a model of the stream and the view. Finally, we began our approach at the micro level. This entailed standardizing the methods of each of these classes. This culminated in closing in on the ideal by applying Qt.io to our PC applications – a synthesis of our Mac OSX and Windows code bases.

Don't miss a Story.
Want to set up a wireless Conference Room?Try Now
The Challenges of VPN, VLAN, UPnP
Posted onAs increasing number of companies are allowing their employees to either work remotely or use their own devices (BYOD) to work from. Consequently, corporate security has become a challenge for IT Administrators. If any security breach occurs due to one of their employees accessing corporate information over an unsecured network, it becomes a nightmare to deal with for the security, network and the IT Admins. In order to avoid dealing with this issue, most enterprises enforce a strict usage of a Virtual Private Network (VPN) for their employees. If they want to access any corporate information, they have to tunnel through a VPN. This is a very secure option for IT Admins as it gives control and a way to manage the network security for employees who are working from a remote location.
However, this results in significant challenges to products that need to be integrated with an enterprise’s network. The developers who work on such products have to take many aspects and intricacies of a VPN into consideration and try to work around the issues that could potentially hinder the performance of the product. While doing so they have to make sure that they make the IT Admins’ life easier and not complicate their job as a result of adding the product to their environment. We at Ubiq have a first hand experience of dealing with VPNs and other network security tools and had to come up with solutions that are not invasive to the corporate environment. To be specific, we had to design our wireless presentation solution in a way that makes both the IT Admin’s and the end-user’s lives easier. Since our solution required users to connect to the Ubiq’s Hive to give a presentation. Any sort of VPN tunneling will prompt the end-user with a security notification that a change in network has occurred. This was an undesirable behaviour. When the entire premise of our solution is simplicity and hassle free. This was not an option for us. On top of this, there are numerous VPN solutions in the market and it was difficult to cater to all of them and make sure that our solution works out of the box. Keeping this in mind, we had to work out a solution that would work regardless of what VPN solution that was in place.
For this, we came up with a solution that used UPnP network discovery protocol which allowed end-users to stream over their corporate network if a Hive is connected to the network. In doing so, we didn’t have to deal with the corporate’s VPN and the IT Admin does not have to worry about dealing any support tickets due to the VPN security notification. UPnP is a fantastic protocol that gave us the flexibility and added performance. The only major issue we had to deal with was the corporate network having multiple subnets or VLANs for their wired and wireless networks. Which is an entirely different problem. Dealing with VPNs was a challenging problem which forced us to think about an alternative solution for corporate users.

Don't miss a Story.
Want to set up a wireless Conference Room?Try Now
Wireless presentations are meant to be collaborative and engaging. Sharing and streaming content from multiple devices without being tethered to wires creates greater access. By using systems, like Ubiq, you and your team are not limited to share with those in the same company. Your guests can be active participants as well.
Here are 5 ways to bring your guests into a wireless presentation:
- Be Proactive: The purpose behind wireless presentations is to empower and promote self-management with little involvement from IT. That doesn’t mean that your IT team shouldn’t be hands-off. Wireless presentations are new to many, and your colleagues need to be trained to use it. They also need to be able to prepare their guests. As they book their meeting space, IT can help teams plan ahead for their meetings by providing instructions, security policy and support for employees and their guests in advance. This will decrease strain on IT and help the meetings run smoother, as hoped.
- Support BYOD: Your guests are not tied to your corporate IT policy when it comes to device and software usage and requirements. However, your policy should make accommodations for them to use their devices on your networks, other than just hardwiring into it. Your BYOD policy should extend to guests by supporting multiple device types and access to your WiFi. If security is a concern, wireless presentations system, like Ubiq, offer data encryption and secured access to ensure the proper parties are connected.
- Collaborate: Turn your presentation into a work session with your guest. Rather than just standing in front of an audience, your guests can engage with your colleagues and stakeholders. That way, they can experience your company’s culture, understand expectations and provide immediate feedback. Wireless presentations make for great brainstorming sessions between you and your vendor, client or partner. Create the opportunity to define your working relationship with them.
- Open Up: When a guest comes into your company, you have to be careful of how much access they should have to your network and data. Closing them off completely can certainly hurt your communication and work exchange. By setting the right security parameters, you can allow guests to connect through a secure WiFi connection and engage in a wireless presentation. For example, Ubiq uses data encryption by session. Therefore, data shared during the presentation is cleared when it has ended. Your goal is to protect your company and its employees, first. However, your policy should extend to include and protect your guests as well.
- Be Remote: Remote presentations are not just for your virtual employees. They can be a great way to work globally with clients and vendors. Larger corporations can benefit as remote presentations can be cost effective and timely. By allowing your guests to lead or engage in a wireless presentation, you can save on travel, collaborate without boundaries and reduce time waste. It allows you to get work completed quicker, which is a plus when working on time-sensitive projects.
Whether it’s a potential vendor or a third-party consultant, their contributions in meetings and conferences should be valuable for your business. Wireless presentations make it possible for them to connect their devices with one simple click and begin sharing. You’ve invited them to your meeting. Let them be fully a part of it.

Don't miss a Story.
Want to set up a wireless Conference Room?Try Now
The world of enterprise technology is evolving at a rapid pace. Cloud computing, and mobile technology are changing the way we work and share information. Data is said to be the “life blood” of an organization. The better your enterprise gets at storing, disseminating, sharing, and securing that data, the more efficient you will be in accomplishing your goals. Here are some suggestions as to why you want to stay ahead of the technology evolution, and what you need to do to stay current.
1) You Need to Embrace Cloud Computing. Cloud computing is similar to an electric power utility in that the providers benefit from economies of scale, and the users benefit from lower usage costs. Users pay for what they consume without investing all that money into infrastructure. With cloud computing, an enterprise can spend less time managing complex IT resources and more time investing in core mission work.
2) The Mobile Workforce Demands Innovative Enterprise Technology. A high percentage of employees are now using two or more mobile devices to get work done. Your enterprise must accommodate and prioritize this new demand for efficiency and productivity as the line between an employee’s personal and professional lives continues to blur. There is an ever increasing demand to adopt cloud-based enterprise mobility strategies, including the concept of personal clouds.
3) Experimentation Cost is Low. In a world where plugging into the latest enterprise technology requires little more than an API, the cost to test new ideas and concepts has never been lower, and the barrier to entry never been easier. This means that if you see an idea that is worth looking at, you probably don’t need to spend a lot of time and money investing in a new infrastructure before you can get an idea of whether the idea is going to work for your enterprise.
4) Keep Your Data Secure. If you are not keeping up with the latest innovations in technology, you are opening yourselves up for increased liability. As mentioned earlier, data is the lifeblood of your business. However, that same data can also be a huge liability if not properly secured. With increased access to data through cloud computing, there is also an increased demand to share that data. You need to stay ahead of the latest innovations so that you can ensure that your data stays secure and so that you are only sharing the segments of data with the appropriate users, and not creating a free-for-all where everybody has access to everything.
5) The “Office” Has Been Redefined. Chances are that your business is not located in one building. You probably have several locations, and you probably have employees working remotely. How do you tie all of this together in one enterprise solution? This is the reality of the modern business world and the challenge facing IT directors. There are innovative conference room technologies and wireless presentation technologies that facilitate all of this remote work, but you must be aware of the latest trends in this aspect of enterprise technology to ensure efficient productivity in your workforce.

Don't miss a Story.
Want to set up a wireless Conference Room?Try Now
The internet and technology continue to allow more and more people to work from home. This creates obvious efficiencies such as eliminating commute time and fuel costs, as well as eliminating the need to find office space for employees that work from home. However, those who have worked from home will attest that eliminating your commute does not automatically translate into an efficient working environment.
There are many obvious ways to encourage efficiency when working from home, including the need to set physical office boundaries as well as boundaries for the time you spend “at work”. There are myriad articles across the internet touching on these efficiencies. Instead, here are 5 tips involving the latest conference room technologies, wireless presentation, and collaboration tools, and that will go a long way to improving your efficiency.
- Enable Calendar Sharing with Colleagues. When you choose to work remotely, it can be very easy to lose touch with what is going on around you. If you work with others on a team who are not physically located in the same place, it becomes even more important to share your calendar. There are many free and paid services (including google) that allow you to see your coworker’s schedules, and allow them to see yours. This makes collaboration so much more efficient by allowing you to see at a glance when a colleague is available for a meeting or to help out on a project.
- Learn to Master Wireless Presentation and Screen Sharing Technology. Remote meetings are pretty much unavoidable when working from home. This is where Ubiq comes to play, we are soon coming out with remote presentation where you can access a presentation from any location. This makes working from home so much easier rather than physically being in meetings. Emails and phone conferences are probably a big part of the day. Some jobs require you to present complex ideas over the phone or through online meetings. Taking the time to learn features and functions of your chosen presentation technology will help you relay your ideas more efficiently. If you can learn to create short, succinct presentations via PowerPoint, video, or by just sharing your screen, you will find it easier to make the sell, or to relay your ideas.
- BROADBAND! This probably goes without saying, but if you work from home, make sure you have the best internet service that you can afford. This is probably the most important tool you have. Nothing kills efficiency like waiting for a page to load, or losing a connection during an important online presentation.
- Invest in the Right Headset, or Microphone and Speakers. If you do spend a lot of time in online meetings, you will want to invest in the right audio visual setup. Just like having the right conference room technology in a physical office, your computer, wireless presentation equipment, and internet connection ARE your conference room. Having the right headset, or microphone will increase the efficiency of your meetings by eliminating disturbing background noise, and other distractions that require you to repeat yourself.
- Consider using apps that track activities and/or manage team projects. There are many online collaboration applications that allow you to segment any project into smaller portions that can be completed by different individuals and then show the combined results in one central location. Many of these applications also provide internal messaging systems for communication back and forth between team members. Constantly updated project information will decrease lag time waiting for replies to emails, or returning phone calls. Everybody’s work is there for all to see in real time.
Don't miss a Story.
Want to set up a wireless Conference Room?Try Now
Implementing new technology can be met with skepticism and fear from colleagues outside of the IT department. With encouragement and a bit of training, those concerns can subside over time. The end result for IT should be to have colleagues feel confident in using new technology without putting a strain on the IT department.
When it comes to communication, especially through wireless presentations, having an easy-to-use tool is key! It reduces the amount of involvement IT needs to have in meeting organization, especially in setting up and/or breaking down conference room hardware and software. The user has more control over the technology and can be his own director in how content is shared through the presentation across devices and platforms.
Wireless presentations are meant to create new means of communication and collaboration across teams. The tools to support them do not need to be complicated. In fact, the purpose of any new technology should be to simply operations. Therefore, IT should seek solutions that will improve upon or create new workflows that benefit the business.
Ubiq’s enterprise solution provides access and security through single sign-on (SSO) and data encryption, all with a simple click. Presentations are activated in 10 seconds or less, empowering the user minimal need for IT assistance. IT team members do not have to be “on call” to manage presentations or provide full audio/visual connection support, unless it’s truly necessary.
With Ubiq, IT resources can review an all-in-one cloud-hosted management dashboard to monitor usage from a central location. The dashboard provides real-time analytics and performance status information to track activities connected to the presentation, down to a specific meeting participant. The ability to conduct performance maintenance checks without having to having to enter a conference room promotes efficiency. There’s no longer the need to manage each individual meeting and the technology supporting it.
Wireless presentations are meant to bring teams together to perform meaningful work without boundaries. That includes your IT team. The team can now be a part of the conversation rather than waiting on the sidelines until someone needs help. It’s time to empower your colleagues and free your IT team to focus on higher priority tasks and projects.
